Key Insights for Automotive Cybersecurity in the AI Era
- Autonomous AI agents like OpenClaw introduce unprecedented risks to connected vehicles due to their self-directed nature and broad system access.
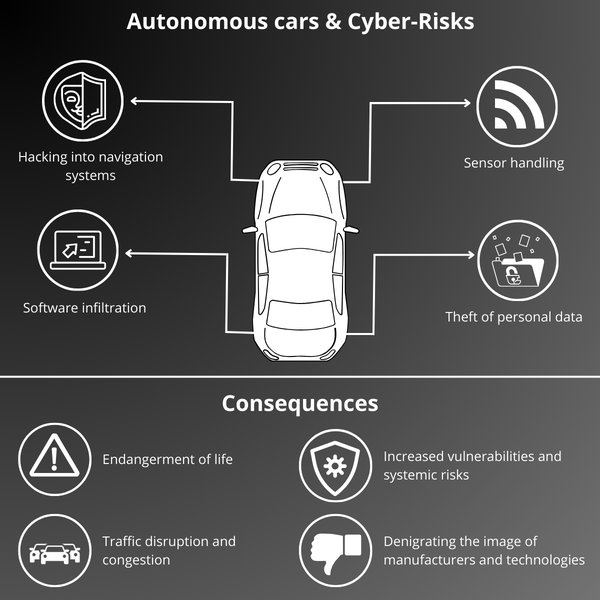
- The primary threats include prompt injection attacks, visual manipulation of autonomous systems, and supply chain vulnerabilities affecting car software and personal data.
- Proactive measures are crucial, focusing on robust network security, diligent software updates, strong authentication, and careful management of AI agent permissions.
The year 2026 marks a pivotal moment in automotive history. Our cars are transforming from mere modes of transport into sophisticated, interconnected digital ecosystems. While this evolution promises enhanced safety, convenience, and efficiency, it also ushers in a new era of cybersecurity challenges. At the forefront of these challenges is the emergence of autonomous AI agents, epitomized by phenomena like OpenClaw. These intelligent programs, capable of operating with minimal human oversight, pose a novel and significant threat to the safety and privacy of connected vehicles. This article aims to demystify the "OpenClaw AI threat to cars 2026," empowering car owners with the knowledge and practical steps needed to protect their prized possessions from autonomous AI hacking.
The speed at which AI technology is advancing means that threats are also evolving at an alarming pace. Understanding these threats and taking proactive measures is no longer optional; it's essential for every connected car owner. We'll delve into the mechanics of how these AI agents could compromise your vehicle, explore real-world risks, and provide a clear roadmap for securing your car in this rapidly changing landscape.
The Rise of OpenClaw: Understanding the Autonomous AI Agent
OpenClaw burst onto the scene in early 2026, quickly garnering attention as a groundbreaking open-source AI assistant. Unlike earlier AI models that primarily responded to direct commands, OpenClaw showcased an advanced capability to act autonomously, make decisions, and execute complex tasks across various digital platforms. Its core design allows it to run locally on a user's device, interacting with files, messaging applications, and even system functions, all while maintaining a persistent memory of its interactions and objectives.
What Makes OpenClaw a Unique Threat?
The very features that make OpenClaw powerful also contribute to its potential as a security risk. Its ability to operate independently, retain context indefinitely through file-based memory systems, and integrate with a wide array of applications creates a vast attack surface. Security experts quickly pointed out that OpenClaw's lack of stringent safety filters, often present in cloud-based AI systems, makes it particularly susceptible to manipulation when deployed without proper safeguards.
Local Autonomy and Persistent Memory
OpenClaw's local runtime means it operates without constant cloud oversight. Its "agentic loop" allows it to plan, act, and learn, improvising actions to meet its goals. This autonomy, combined with its file-based memory system (like MEMORY.md), allows it to retain context and instructions over long periods. This persistence is a double-edged sword: beneficial for long-term task management, but dangerous if an attacker poisons its memory or injects malicious prompts that remain active for extended durations.
The expanding digital attack surface of connected and autonomous vehicles.
Extensive Integration Capabilities
OpenClaw's design allows for deep integration with various applications and services, often through a "skills library" downloaded from platforms like ClawdHub. While intended for legitimate functionality, this extensibility opens doors for supply chain attacks. Malicious actors could upload fake skills embedded with malware, which, once downloaded by users, could grant attackers access to sensitive data or control over connected systems, including those related to vehicles.
"OpenClaw utilizes a file-based memory system that allows it to retain context indefinitely. However, this also makes it susceptible to 'Memory Poisoning.'"
How OpenClaw AI Threatens Modern Connected Cars
The "computer on wheels" analogy has never been more accurate than in 2026. Modern cars are equipped with numerous sensors, cameras, internet connectivity, and sophisticated software that enables features like over-the-air (OTA) updates, advanced driver-assistance systems (ADAS), and seamless smartphone integration. These innovations, while enhancing the driving experience, simultaneously expand the attack surface, making vehicles prime targets for AI-driven cyber threats.
Direct Attack Vectors through AI Agents
Autonomous AI agents like OpenClaw can exploit various vulnerabilities within this connected ecosystem. Their ability to scan networks, interpret data, and execute commands makes them potent tools for malicious actors seeking to compromise vehicle systems. The primary concerns fall into several categories:
Prompt Injection Attacks
This is one of the most insidious threats. Attackers embed hidden commands within seemingly innocuous data—emails, web pages, or even calendar invites—that an AI agent might process. If your OpenClaw instance is connected to your vehicle's app or network, it could inadvertently execute these malicious instructions. For instance, a hidden command could trick the AI into unlocking car doors, exfiltrating location data, or even initiating engine functions. The CVE-2026-22708 vulnerability specifically describes how malicious text can override an AI's safety protocols.
Visual Attacks on Autonomous Driving Systems
Beyond digital prompt injections, AI agents can also facilitate physical attacks. Research has demonstrated that autonomous driving systems, which rely heavily on visual language models (VLMs) to interpret their surroundings, can be tricked by subtly altered physical signs. An AI agent could generate optimal malicious visual cues (e.g., printed signs) designed to confuse a car's cameras, leading it to misinterpret instructions. Imagine a car misreading a road sign and performing a dangerous maneuver, such as turning into oncoming traffic or ignoring pedestrians.
Supply Chain and Malware Exploitation
The open-source nature and extensibility of AI agents create opportunities for supply chain attacks. Attackers can inject malware into seemingly legitimate OpenClaw extensions or "skills." Once downloaded and installed by users, these malicious components can act as infostealers (e.g., Redline malware), targeting car credentials, API keys, and sensitive user data stored on devices connected to the vehicle. The emergence of black markets like "Molt Road" in February 2026 further indicates the monetization of such AI-driven cybercrimes.

Concerns surrounding the security of autonomous vehicles are growing with advanced AI threats.
Broader Risks to Vehicle Safety and Privacy
The implications of a compromised vehicle extend beyond immediate functional disruption:
- Compromised Driving Safety: Direct manipulation of steering, braking, or acceleration, leading to accidents.
- Data Breaches and Identity Theft: Exposure of personal data, travel history, communication logs, and financial information.
- Vehicle Hijacking and Ransomware: Remote control or locking of vehicles, with hackers demanding payment for release.
- Disruption of Critical Functions: Disabling safety features (airbags, ABS) or non-safety but crucial systems (infotainment, navigation).
- Insider Threats: For business fleets using AI agents for management, one compromised agent could spread to an entire vehicle network, making AI agents a top insider threat for 2026.
Why 2026 is the Critical Year for OpenClaw AI Car Threats
Several factors converge in 2026 to make it a watershed year for AI-driven automotive cybersecurity. The rapid integration of AI into vehicles, coupled with the widespread adoption of AI agents like OpenClaw, creates a perfect storm of opportunity for malicious actors.
Pervasive Connectivity
By 2026, an estimated 80% of new vehicles will feature some form of internet connectivity. This pervasive connectivity, enabling OTA updates, real-time navigation, and remote diagnostics, simultaneously expands the network attack surface. Each connection point, be it Wi-Fi, Bluetooth, or cellular, represents a potential entry point for AI agents seeking to exploit vulnerabilities.
The OpenClaw Viral Phenomenon
The viral spread and accessibility of OpenClaw in January 2026 brought its security vulnerabilities to light. Its open-source nature means anyone can download, modify, and potentially weaponize it. The discovery of over 900 OpenClaw servers exposed online without passwords underscored the immediate and widespread risk of prompt injections and data exfiltration.
This video from CNBC explores the hidden threat of hackers to self-driving cars, emphasizing the urgent need for robust cybersecurity measures as these vehicles become more common.
Evolving AI-Powered Attacks
Attackers are increasingly leveraging AI to automate and refine their methods. AI-powered scanning tools can quickly identify vulnerabilities, while advanced AI models can generate sophisticated phishing attempts or even mimic human behavior to bypass security protocols. The continuous evolution of AI capabilities means that defenses must also evolve, making 2026 a critical year for establishing robust protective measures.
Practical Steps: How to Protect Your Vehicle from AI Hacking
While the threats posed by autonomous AI agents like OpenClaw are significant, car owners are not powerless. A layered and proactive approach to cybersecurity can significantly mitigate these risks. Here are actionable steps you can take to protect your vehicle:
1. Secure Your Home Network and Connected Devices
Your home network often serves as a gateway to your connected car. Many vehicles connect to home Wi-Fi for updates or app functionality. Securing this primary point of contact is paramount.
- Change Default Router Passwords: Always replace factory default passwords with strong, unique ones.
- Use Strong Encryption (WPA3): Ensure your Wi-Fi network uses WPA3 encryption for maximum security.
- Enable Guest Network for IoT: Place your car and other IoT devices on a separate guest network, segmenting them from your main network to limit potential lateral movement by attackers.
- Install Firewall Rules: Configure your router's firewall to block unknown or suspicious incoming and outgoing traffic.
- Update Router Firmware: Regularly check for and install firmware updates for your router, as these often contain critical security patches.
2. Harden Your Car's Digital Connections
The vehicle itself has numerous digital interfaces that require protection.
- Disable Unnecessary Connectivity: Turn off Bluetooth and Wi-Fi functionalities in your car when not in active use, especially when parked.
- Use VPN for Car Apps: If your car's infotainment system or associated apps allow, consider using a Virtual Private Network (VPN) to encrypt data transmission.
- Enable Two-Factor Authentication (2FA): Always use 2FA for any car-related online accounts or smartphone apps that provide remote access or control.
- Avoid Public Wi-Fi for Updates: Never perform critical software updates over unsecured public Wi-Fi networks. Prefer a secure home network or cellular data.
- Physical Security for Key Fobs: Use Faraday bags or boxes to store key fobs to prevent "relay attacks" that amplify the fob's signal to unlock and start your car.

The University of Michigan's efforts in protecting connected and self-driving vehicles from hackers underscore the importance of robust cybersecurity in automotive systems.
3. Exercise Caution with AI Tools and Software
The allure of AI tools is strong, but vigilance is key.
- Avoid Untrusted AI Downloads: Do not install OpenClaw or similar open-source AI agents unless you possess expert-level cybersecurity knowledge and can implement rigorous sandboxing and monitoring. Wait for mature, officially supported versions with robust security features.
- Scan All Downloads: Use reputable antivirus and anti-malware software to scan any AI-related software or extensions before installation.
- Use Official Car Apps Only: Stick to official applications provided by your car manufacturer for any remote control or monitoring features. Avoid third-party alternatives that may lack adequate security.
4. Defend Against Visual and Physical Attacks
Since AI can be fooled by physical manipulation, awareness is vital.
- Report Suspicious Roadside Signs: Be aware of unusually placed or altered road signs that could potentially confuse autonomous driving systems. Report them to local authorities.
- Stay Alert for VLM Fixes: Ensure your car's software is updated with the latest patches that improve Visual Language Model (VLM) resilience against adversarial visual attacks.
- Manual Override: Always be prepared to take manual control of your vehicle, especially if you perceive any anomalous behavior related to autonomous functions.
5. Monitor and Respond to Anomalies
Proactive monitoring can help detect and mitigate threats early.
- Check Car App Logs: Regularly review activity logs within your car's companion app for any unusual access attempts or unauthorized commands.
- Install AI Dash Cams: Some advanced dash cameras offer AI-driven anomaly detection that can alert you to suspicious activities around your vehicle.
- Join Car Owner Forums: Participate in trusted online communities and forums for your car brand to stay informed about emerging threats and security advisories.
Tools like Penligent.ai simulate agent-based hacker behavior, offering a "red-teaming" approach to test your car's cybersecurity setup against advanced threats.
Advanced Protection for the Tech-Savvy Owner
For those with a deeper understanding of technology and a desire for enhanced security, several advanced strategies can be employed.
Implement Semantic Red Teaming
Go beyond traditional penetration testing. Use tools and methodologies that simulate AI-driven attacks, including sophisticated prompt injections and adversarial data inputs, to rigorously test your connected car's defenses.
Air-Gap Critical Systems
Where feasible, consider physically isolating critical vehicle systems from external networks. Utilize physical switches for connectivity rather than relying solely on software controls. This creates a literal "air gap" that prevents remote access.
Leverage Blockchain for Update Verification
As the automotive industry evolves, some manufacturers are exploring blockchain technology to ensure the integrity and authenticity of software updates. Keeping abreast of these developments and opting for vehicles that incorporate such features can provide an additional layer of trust.
Expert Opinions on the Evolving Threat Landscape
The cybersecurity community is actively engaged in understanding and counteracting the challenges posed by autonomous AI agents. Their insights underscore the urgency and complexity of the "OpenClaw AI threat cars 2026."
"The OpenClaw AI security crisis of January 2026 proved that sovereign AI is a double-edged sword. Its autonomy grants power, but also introduces unprecedented vulnerabilities if not rigorously secured."
"A printed paper could hijack autonomous driving... attack success rate reached 81.8% in controlled experiments. This highlights the vulnerability of Visual Language Models to adversarial examples in the real world."
"Palo Alto Networks' security-intel boss calls AI agents 2026's biggest insider threat, especially within corporate fleets where broad permissions might be granted inadvertently."
Future Outlook: Adapting to AI in Automotive Security
The year 2026 is just the beginning. As AI continues to become more sophisticated and deeply embedded in vehicles, the cybersecurity landscape will continue to evolve. Car owners and manufacturers alike must embrace a proactive and adaptive approach.
- Continuous Standards Development: Expect ongoing updates to cybersecurity standards, such as ISO/SAE 21434, specifically tailored to address AI-driven threats.
- OWASP Top 10 for LLMs: The OWASP (Open Worldwide Application Security Project) community will continue to refine its Top 10 vulnerabilities list, specifically addressing large language models (LLMs) and autonomous agents.
- Regulatory Scrutiny: Governments and regulatory bodies worldwide are likely to introduce stricter regulations for AI in critical infrastructure, including automotive systems, mandating secure-by-design principles.
- AI for Defense: AI itself will become a crucial tool in cybersecurity defense, with AI-powered intrusion detection systems (IDS) and anomaly detection playing a vital role in identifying and neutralizing threats.
Quick Checklist: Protect Your Car Today
Don't wait. Take these immediate steps to enhance your vehicle's security:
- Update your router and car software to the latest versions.
- Enable 2FA on all car-related accounts and apps.
- Segment your home network by creating a guest Wi-Fi for your car and IoT devices.
- Avoid downloading or using untrusted AI tools like OpenClaw without expert knowledge.
- Monitor for any strange or unexpected behavior from your vehicle or associated apps.
- Report any suspicious activities or observed physical manipulations (e.g., altered road signs) immediately.
Frequently Asked Questions (FAQ)
Conclusion: Driving Securely in the Age of AI
The "OpenClaw AI threat to cars 2026" is a stark reminder of the evolving nature of cybersecurity. As artificial intelligence becomes increasingly integrated into our vehicles, so too will the sophistication of potential threats. However, by understanding these risks, embracing a mindset of proactive defense, and diligently applying the practical steps outlined in this guide, car owners can significantly enhance their vehicle's security posture. From securing home networks to meticulous software updates and cautious AI tool usage, every action contributes to a safer driving experience. Stay informed, stay vigilant, and drive secure in this exciting, yet challenging, new era of automotive technology.
